Showing all 7 resultsSorted by latest
Comprehensive Guide to Access Control
Access control is a fundamental component of physical and cybersecurity. It determines who may access the resource, when, and under what circumstances. In this page, you are going to find answers to the most important Access Control questions, learning what are its different types, implementation ways, how it relates to authentication, what is physical access control, and more about its relevance on various applications. If you are new to this topic, we recommend reading our detailed guide ” What Is An Access Control System?” to understand the fundamentals, core concepts, and how access control systems work in modern environments.
We also share our expertise on Access Control Products, leading Access Control Systems, and Access Control Solutions with the most qualified selections for your company.
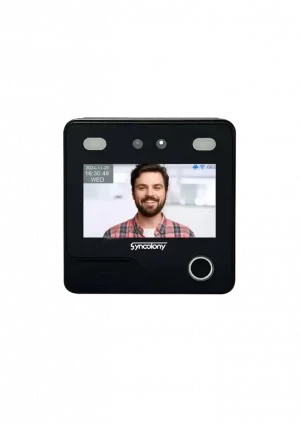
Explore top Syncolony Access Control Products, Solutions, and Systems to secure your assets effectively.
Authentication vs. Authorization
It is crucial to distinguish authentication from authorization: This could be a password or a security-based biometric device.
• Authorization: Determining what an authenticated user can do. To put it simply, authentication is asked with the question “Who are you?” and authorization is asked “What are you allowed to do?” Both are required in every access control system.
What Is Physical Access Control?
These are the systems and procedures designed to limit access to spaces and locations with a physical presence, such as offices, laboratories, data centers, and areas that are restricted. Physical access control systems, which are digital in nature, provide coverage for people, assets, and sensitive areas and provide a protective control layer.
Why Do We Need Access Control?
Access control is important for several reasons:
• Security: Users will not be allowed to access resources they are not authorized to access.
• Data Security: Sensitive data is exposed only to authorized users.
• Compliance: Adherence to standards and regulations (e.g., GDPR, HIPAA, ISO).
• Efficient Operations: Simplifying the access management process with less manual handling.
Without leading access control software, organizations face breaches, data loss, and risk exposure.
Access Control in Different Fields
Enterprise IT
• Protecting digital resources, applications, and networks.
• Effective management of user roles and permissions in an access control system.
For organizations looking to implement access control strategically, explore our in-depth article on “How to Choose the Best Access Control System for Your Business” to learn how companies can improve security, compliance, and operational efficiency through smart access management.
Science R&D and AI
• Protects sensitive datasets and AI models.
• Facilitates regulated collaboration among researchers through access control mechanisms.
Physical Security
• Access control solutions are used to protect facilities, laboratories, and key infrastructure.
• Keeps track of people for security and regulation purposes.
Cloud and Hybrid Environments
• Delivers a centralized access control mechanism for disparate systems.
• Facilitates dynamic, context-sensitive access based on user, device, and location.
Physical Identity and Access Management (PIAM)
Physical Identity and Access Management (PIAM) combines physical security and identity management. It verifies that access credentials of individual users are authenticated, authorized, and audited. PIAM solutions consolidate:
• Personnel records
• Access permissions
• Audit trails (for compliance and accountability)
This combination delivers a full security picture and includes features such as efficiency, integration, and best access control systems
Global Access Control Management the Easy Way
Next-generation access control systems have cloud-based management tools that ease the administration of access security across multiple international locations. Advantages include:
• Unified user and device management dashboard
• Real-time monitoring of access events
• Support for access control hardware and software integration
Through Syncolony access control solutions, enterprises are able to simplify administration and deliver more consistent security.
5 Types or Models of Access Control
Access control can be defined using the following models:
- Discretionary Access Control (DAC): Permissions are granted by the resource owner.
- Mandatory Access Control (MAC): Permissions are mandated by central policies.
- Role-Based Access Control (RBAC): Users have access based on their role.
- Attribute-Based Access Control (ABAC): Access decisions based on attributes of the user, the resource, and the environment.
- Rule-Based Access Control: Access is allowed or denied based on dynamic rules like time, location, or device.
Benefits of Access Control Systems
The benefits of implementing the best access control systems in your organization include:
• Superior security for both physical and digital assets.
• Simplified user, device, and permission management.
• Real-time monitoring and auditing for compliance.
• Minimized risk of data breaches and internal threats.
• Scalability as organizations expand.
Applications of Access Control
Access control systems are commonly available for use in:
• Corporate offices: Secure entry and IT access.
• Research labs: Protection of sensitive experiments and datasets.
• Healthcare: Regulated access to patient records and restricted zones.
• Cloud services: Controlling user access to SaaS applications and network resources.
• Industrial environments: Machinery and vehicle access, plus security in industrial areas.
By combining Access Control Software, Access Control Device, and Smart Gates, organizations can have a complete and effective security ecosystem.
The Value of Access Control
Access control offers both tangible and intangible benefits, including:
• Security: Deters unauthorized access and safeguards resources.
• Compliance: Ensures adherence to legal and regulatory standards.
• Accountability: Tracks who accessed what, when, and how.
• Streamlined Operations: Reduces paperwork and automates access management.
• Scalability: Adapts to organizational growth and evolving needs.
Choosing top access control systems guarantees superior protection and operational efficiency.
How Does an Access Control System Operate?
A high-level Access Control System operates via three fundamental steps:
- Identification: The user claims an identity (via card, biometric, or PIN).
- Authentication: The provided credentials are validated against a secure database.
- Authorization: The system decides whether to grant access and logs the event.
This process applies to both physical and digital access control systems.
Your Access Control Software and hardware should integrate seamlessly with your Smart Gate Entrance to ensure smooth and secure operations.
Looking for more insights?
• Learn the fundamentals in What Is An Access Control System?
• Discover business strategies in How to Choose the Best Access Control System for Your Business